Apple denied it
Apple strongly denies bombshell report that Chinese spies were able to secretly implant chips in its servers (AAPL)
Kif Leswing,Business Insider 6 hours ago
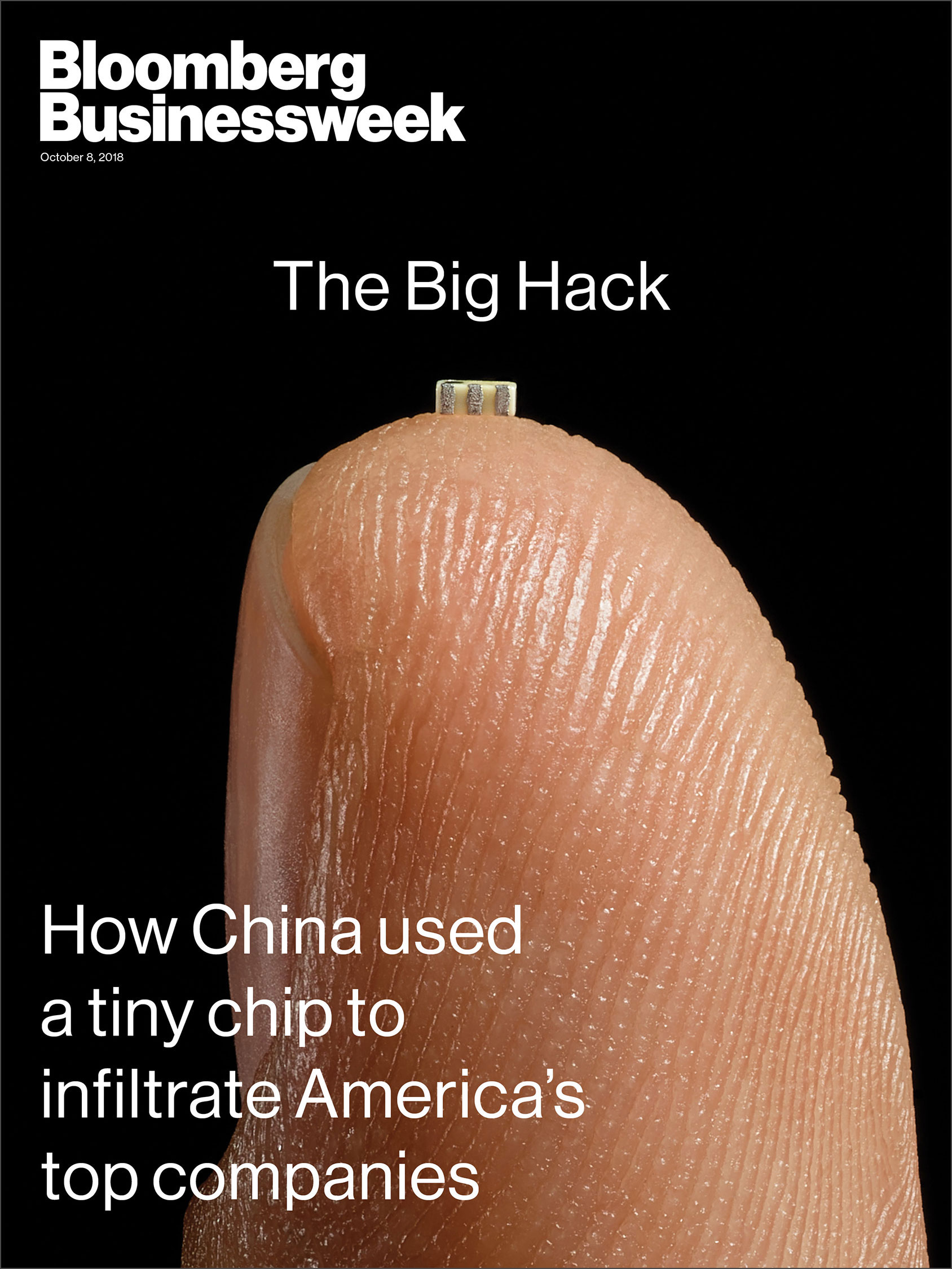
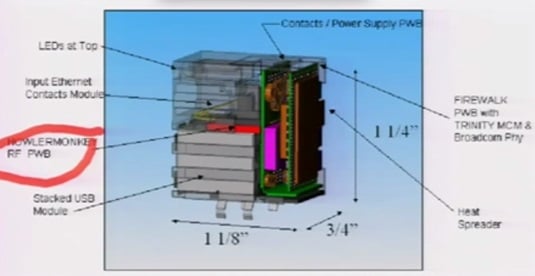
- Chinese spies were able to add small, undocumented chips to motherboards in data servers bought by big US tech companies, according to a blockbuster investigation by Bloomberg published Thursday.
- Apple denies that it has ever found malicious chips in its servers.
- Apple also denies that it is under a national security "gag order," undercutting speculation that it was under pressure from the government to deny the Bloomberg report.
On Thursday,
that found that Chinese spies were able to plant tiny microchips on motherboards in data servers supplied by SuperMicro to a slew of American tech companies, including Apple.
The goal of the Chinese spies was reportedly to use these microchips to gain access to sensitive corporate data and other secrets through advanced hacking, according to Bloomberg
Apple is denying just about every fact in
which says it discovered suspicious chips in its servers in 2015.
In a statement
on Thursday afternoon Apple says that the company has never found any "malicious chips" or vulnerabilities in "any server" and completely denies having any contact with the "FBI or any other agency about such an incident" — directly refuting several key claims in the report.
"Despite numerous discussions across multiple teams and organizations, no one at Apple has ever heard of this investigation," according to Apple's updated statement on Thursday, which said it was first contacted by Bloomberg's reporters about the alleged FBI investigation in November 2017.
It's a pretty unequivocal denial. However, there was speculation after the original report and denial was released on Thursday that Apple could be under a gag order — a possible way to reconcile Bloomberg's reporting with Apple's denial.
Certain federal investigations dealing with espionage and national security can issue such orders, which preclude the recipient from even discussing the existence of the order. The most common version is called a "
"
But Apple is denying that too, in an updated statement issued later on Thursday, that it is under any gag order:
"Finally, in response to questions we have received from other news organizations since Businessweek published its story, we are not under any kind of gag order or other confidentiality obligations."
It's a difficult situation to reconcile. Bloomberg is a reputable news outlet with a history of breaking big stories, and has revealed conspiracies of this size and scope in the past. In a statement to Business Insider earlier on Thursday, Bloomberg said that it stood by its reporting, which cited 18 unnamed sources.
But Apple — and other companies involved, including Amazon — have all made strongly worded statements completely denying the facts reported by Bloomberg. For its part, Amazon said that it's "
" the inaccuracies in the Bloomberg story.
Given that these companies are publicly traded and this kind of information is clearly material to its stock price, any falsehoods in statements like these could land it in trouble with federal authorities.
Of note: In 2017, Apple
downloading infected firmware that was related to servers manufactured by SuperMicro.
So it's a difficult situation to clearly parse and understand at the moment — perhaps not surprising, given that the story involves some of the most shadowy realms in the world, touching both American and Chinese spies, high-tech manufacturing, and hacking.
Apple's full statement is reproduced below:
The October 8, 2018 issue of Bloomberg Businessweek incorrectly reports that Apple found “malicious chips” in servers on its network in 2015. As Apple has repeatedly explained to Bloomberg reporters and editors over the past 12 months, there is no truth to these claims.
Apple provided Bloomberg Businessweek with the following statement before their story was published:
Over the course of the past year, Bloomberg has contacted us multiple times with claims, sometimes vague and sometimes elaborate, of an alleged security incident at Apple. Each time, we have conducted rigorous internal investigations based on their inquiries and each time we have found absolutely no evidence to support any of them. We have repeatedly and consistently offered factual responses, on the record, refuting virtually every aspect of Bloomberg’s story relating to Apple.
On this we can be very clear: Apple has never found malicious chips, “hardware manipulations” or vulnerabilities purposely planted in any server. Apple never had any contact with the FBI or any other agency about such an incident. We are not aware of any investigation by the FBI, nor are our contacts in law enforcement.
In response to Bloomberg’s latest version of the narrative, we present the following facts: Siri and Topsy never shared servers; Siri has never been deployed on servers sold to us by Super Micro; and Topsy data was limited to approximately 2,000 Super Micro servers, not 7,000. None of those servers have ever been found to hold malicious chips.
As a matter of practice, before servers are put into production at Apple they are inspected for security vulnerabilities and we update all firmware and software with the latest protections. We did not uncover any unusual vulnerabilities in the servers we purchased from Super Micro when we updated the firmware and software according to our standard procedures.
We are deeply disappointed that in their dealings with us, Bloomberg’s reporters have not been open to the possibility that they or their sources might be wrong or misinformed. Our best guess is that they are confusing their story with a previously-reported 2016 incident in which we discovered an infected driver on a single Super Micro server in one of our labs. That one-time event was determined to be accidental and not a targeted attack against Apple.
While there has been no claim that customer data was involved, we take these allegations seriously and we want users to know that we do everything possible to safeguard the personal information they entrust to us. We also want them to know that what Bloomberg is reporting about Apple is inaccurate.
Apple has always believed in being transparent about the ways we handle and protect data. If there were ever such an event as Bloomberg News has claimed, we would be forthcoming about it and we would work closely with law enforcement. Apple engineers conduct regular and rigorous security screenings to ensure that our systems are safe. We know that security is an endless race and that’s why we constantly fortify our systems against increasingly sophisticated hackers and cybercriminals who want to steal our data.
The published Businessweek story also claims that Apple “reported the incident to the FBI but kept details about what it had detected tightly held, even internally.” In November 2017, after we had first been presented with this allegation, we provided the following information to Bloomberg as part of a lengthy and detailed, on-the-record response. It first addresses their reporters’ unsubstantiated claims about a supposed internal investigation:
Despite numerous discussions across multiple teams and organizations, no one at Apple has ever heard of this investigation. Businessweek has refused to provide us with any information to track down the supposed proceedings or findings. Nor have they demonstrated any understanding of the standard procedures which were supposedly circumvented.
No one from Apple ever reached out to the FBI about anything like this, and we have never heard from the FBI about an investigation of this kind — much less tried to restrict it.
In an appearance this morning on Bloomberg Television, reporter Jordan Robertson made further claims about the supposed discovery of malicious chips, saying, “In Apple’s case, our understanding is it was a random spot check of some problematic servers that led to this detection.”
As we have previously informed Bloomberg, this is completely untrue. Apple has never found malicious chips in our servers.
Finally, in response to questions we have received from other news organizations since Businessweek published its story, we are not under any kind of gag order or other confidentiality obligations.